According to Verizon's 2025 Data Breach Investigations Report, phishing is involved in 80-95% of all successful cyberattacks. It is the single most common entry point for data breaches, ransomware infections, and financial fraud. It works because it targets the human element, not systems. That is why phishing awareness training is crucial.

Phishing awareness training turns an organization's greatest vulnerability into its strongest line of defense. No firewall or antivirus alone can detect and block a convincing phishing email.This phishing awareness training and education guide addresses the following:
- How phishing works,
- How phishing awareness training prevents cyberattacks,
- What every major phishing attack looks like,
- How to spot and report suspicious emails/messages,
- What to do if you've already been phished,
- And how to build a phishing awareness training program that actually changes behavior.
This guide serves both security professionals building a security awareness trainingprogram from scratch and everyday users seeking to recognize and avoid phishing threats.
Just getting started with phishing awareness training? Adaptive Security helps you launch a complete program without starting from scratch.
What Is Phishing Awareness Training?
Phishing awareness training is a structured cybersecurity awareness program that teaches individuals and employees to recognize, avoid, and report phishing emails. It combines educational content, covering how attacks work, what they look like, and why they succeed, with practical exercises like phishing email simulations that test real-world responses under realistic conditions.
A typical phishing awareness training program covers multiple attack channels:
- Email phishing: Malicious links, fake login pages, and attachment-based attacks
- Smishing: SMS messages designed to trigger urgency or curiosity
- Vishing: Voice calls that impersonate trusted individuals or organizations
- AI-driven phishing: Highly personalized messages generated at scale with near-perfect language
The goal of phishing awareness training is to prepare everyone to be a part of the defense system against phishing attacks, not the targets.
Why Does Phishing Awareness Training Matter?
Most cyberattacks start with a manipulative social engineering tactic, rather than a technical exploit. According to Verizon DBIR 2025, 60% of breaches involved the human element, with phishing accounting for 16% of initial breach vectors.
This indicates that phishing awareness training is no longer optional, but rather a full-fledged cyberattack prevention method that is worth practicing.
Research consistently shows that phishing awareness training alone reduces 90% of data breaches when implemented as a continuous, simulation-based program rather than a perfunctory annual compliance exercise. According to KnowBe4's 2024 Phishing by Industry Benchmarking Report, organizations that run monthly phishing simulations see employee click rates drop from an industry baseline of ~30% to below 5% within 12 months.
However, it needs to be implemented quickly, as generative AI has made it trivially easy to send mass-generated, hyper-personalized phishing emails at scale. Any phishing awareness training program that hasn't been updated to detect and combat AI-generated phishing attacks is already outdated.
AI-powered phishing attacks are already here. Train your team to recognize and stop them before they cause real damage.
How Phishing Awareness Training Helps Prevent Cyber Attacks
The psychology behind phishing awareness training is simple: pause and verify before taking any action.
Phishing scams take advantage of the human impulse to take action on personalized and urgent messages. Phishing awareness training aims to break that cycle by introducing the instinct to double-check everything before taking any action on the phishing email.
The friction created by phishing awareness training allows the person on the receiving end to:
- Check the sender domain carefully
- Verify links, attachments, and sender identities
- Question unexpected requests
- Verify sensitive actions through a third-party channel
Phishing awareness training also builds a report-first culture. Organizations where employees actively report suspicious emails give security teams early warning of live phishing campaigns, prompting action often before a single credential is compromised.
Detection speed is one of the largest cost drivers in breach response. The faster you can detect a breach attempt, phishing attack or not, the less damaging the breach is.
The Biggest Benefits of Running Regular Phishing Awareness Training
Phishing awareness training is effective in phishing attack prevention in a way that general cybersecurity awareness training programs can't target.
Regular phishing awareness training reduces a measurable amount of your organization's attack surface. It also creates a documented, auditable security practice that satisfies requirements under HIPAA, PCI-DSS, ISO 27001, and increasingly, cyber insurance policy conditions.
These are the benefits of running a phishing awareness training program regularly:
- Phishing awareness training builds instinctive threat recognition and confidence in handling suspicious communications.
- Phishing awareness training reduces human-error breaches and the resulting financial losses from fraud (fake invoices, credential theft).
- Phishing awareness training strengthens a security-first culture and reduces overdependence on IT by empowering employees as a first line of defense.
- Phishing awareness training keeps everyone updated on evolving phishing scams, including AI-generated emails, impersonation, and BEC.
- It improves incident reporting speed, enabling quicker containment and less operational downtime.
- Phishing awareness training reinforces safe password practices and encourages multi-factor authentication (MFA).
- It helps protect sensitive business and personal data from unauthorized access.
Apart from the aforementioned benefits, phishing awareness training also lowers long-term cybersecurity costs by preventing attacks rather than reacting to them after the damage has already been done.
Reduce breach costs before they start. Adaptive Security turns phishing awareness training into measurable financial protection.
Core Principles & Fundamentals of Phishing Awareness Training
Effective phishing awareness training starts with understanding why phishing works. Cyber attackers exploit urgency, authority, and trust. Phishing mail, SMS (smishing), voice calls (vishing), BEC, and social media impersonation all rely on the same core tactics, delivered through different channels.Modern phishing awareness training relies on phishing simulations, short-form microlearning, and role-based phishing attack scenarios that reflect real job responsibilities.
These are the core principles and fundamentals everyone should learn to make phishing awareness training more effective:
- Understand attacker psychology: Recognize how urgency, authority, and trust are exploited in emails, SMS, voice calls, BEC, and social media impersonation.
- Develop verification habits: Always check sender identities, hover over links, and handle attachments cautiously.
- Practice through simulations: Regular, realistic phishing exercises let the trainee apply their skills safely.
- Use role-based scenarios: Tailor training to reflect specific job responsibilities for relevance and engagement.
- Leverage microlearning: Short, focused lessons improve retention and reduce cognitive overload.
- Maintain reinforcement cadence: Frequent reminders and refreshers prevent skills from fading and ensure long-term behavior change.
Phishing Awareness Training for Employees vs. General Users
Employees and general users face very different phishing threats, which means phishing awareness training needs to be tailored. Employees encounter organization-specific attacks like business email compromise (BEC), payroll fraud, and credential harvesting. Effective training for them is structured, recurring, and role-based, often including simulations.
General users are targeted by scams such as fake banking alerts, delivery notices, or account verification messages. Strong personal habits, like checking links and enabling MFA, improve both personal and workplace security.
Phishing Awareness Training for Specific Industries
Each industry presents its own challenges in implementing effective phishing awareness training.
- Healthcare faces HIPAA compliance challenges, medical record theft, and ransomware targeting hospitals.
- Finance deals with wire fraud, credential theft, and regulatory pressure.
- Education struggles with high student turnover, under-resourced IT teams, and frequent credential phishing.
- Government offices contend with spear phishing and nation-state attacks.
According to StationX 2026, financial institutions face 27.7% of attacks, SaaS 17.7%, and social media 10.4%. After 12 months of phishing awareness training, finance sector click-through success rates hit 74%, while healthcare and retail reach about 61%.
How Does a Phishing Attack Work? (Step by Step) - Phishing Awareness Training Explanation
Phishing awareness training teaches participants that attacks never begin with a system vulnerability. Cyber attackers start by analyzing who is the easiest person to target within an organization. The context they gather during this process is what makes the phishing attack believable.
Once the target is clear, the attacker builds a convincing lure designed to trigger action. Depending on the person's role/data, that could be a password reset request, an invoice, a login alert, or a message from "the manager" asking for something urgent. They generate just enough pressure or familiarity to prompt action before verification can occur.
The target is hit by the phishing attack at a time to match real workflows like end-of-day approvals or busy mornings. According to the Cofense 2026 report, phishing emails were being sent every 19 seconds in 2025, which means these attacks are constant, not occasional.
Once the target interacts with the email in any way, such as clicking a link, downloading an attachment, or responding to the email, the cyber attacker moves on to the next step.
Most often, they use the stolen credentials to access their targeted system. According to Verizon's 2025 DBIR, stolen credentials were involved in 22% of breaches. Once inside, phishing attackers expand access, escalate privileges, and move laterally across systems until they reach something valuable.
From there, the damage phase starts. It can be anywhere from data exfiltration, ransomware deployment, to financial fraud or internal impersonation (also called BEC in organizational environments) to continue the attack chain.
Phishing awareness training changes the outcome. It interrupts the attack at the only stage where the target has control: before the click.
Stop phishing attacks at the only stage that matters. Adaptive Security trains your employees to catch phishing threats before the click.
What Are the Different Types of Phishing Attacks? Phishing Awareness Training Guide
Phishing awareness training in cybersecurity isn't one-size-fits-all. Attackers adapt based on target and effort. Key types of phishing attacks include:
- Email phishing: Mass attacks with generic messages promising prizes, urgent alerts, or fake invoices sent to thousands at once.
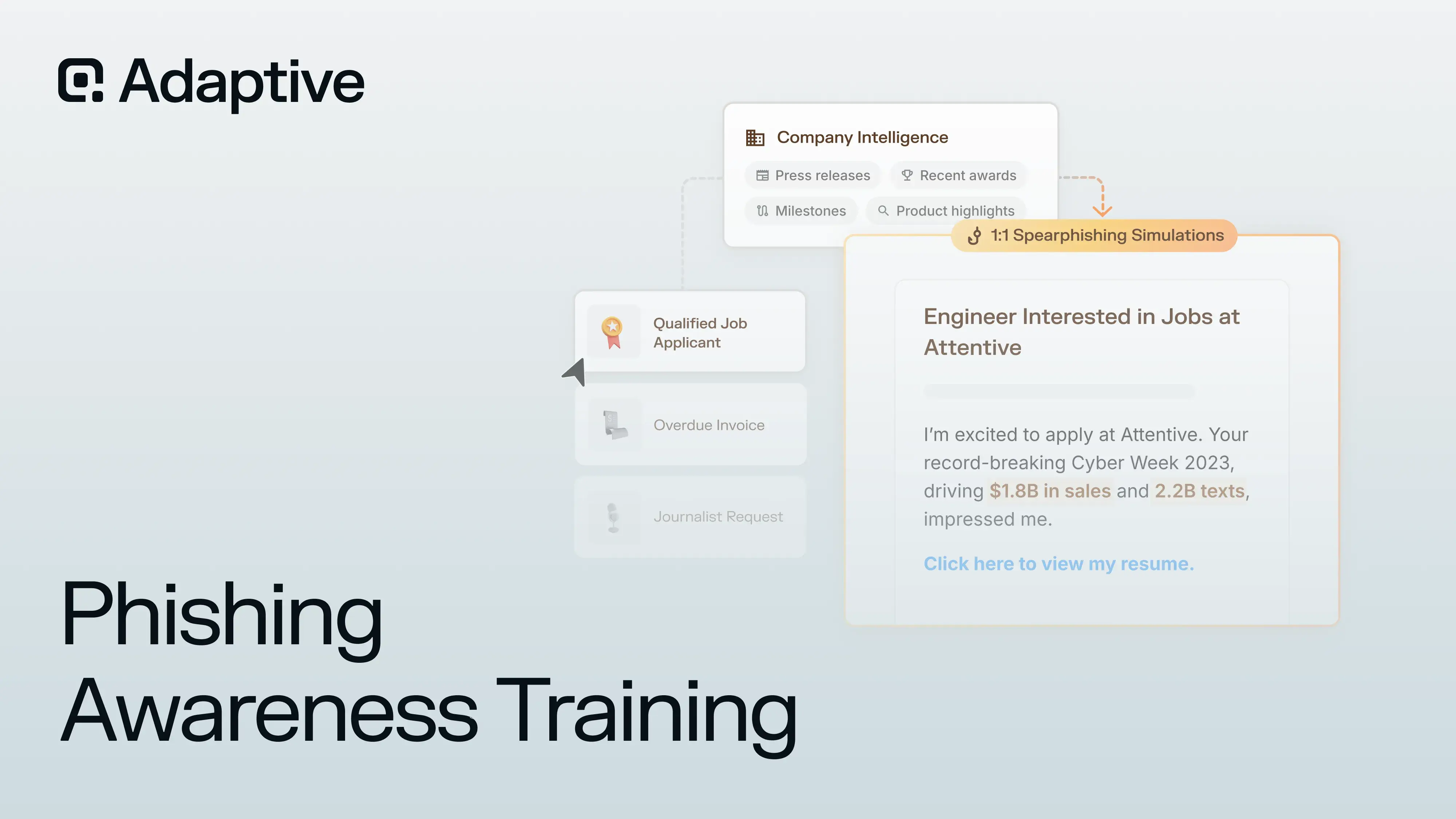
- Spear phishing: Highly targeted messages using personal or company information to appear legitimate.
- Whaling: Focuses on executives and C-suite personnel. It usually exploits high-level responsibilities like approving financial transfers.
- Smishing: Malicious links or urgent prompts delivered via SMS. Feels more personal, but it is the same as phishing emails.
- Vishing: Voice calls, now equipped with AI-cloned voices, impersonating trusted contacts.
- Clone phishing: Duplicates legitimate emails you've received, swapping in malicious links or attachments.
- Angler phishing: Fake social media support accounts designed to steal credentials or financial info.
- AI-powered phishing: Hyper-personalized emails or messages created at scale using AI, often bypassing traditional filters and mimicking tone, language, and context of trusted contacts.
Each type differs in delivery, personalization, and target, which is why phishing awareness training focuses on recognizing both the content and the method behind the phishing attack.
Phishing Awareness Training Insights: Spear Phishing & Why Targeted Attacks Are the Most Dangerous
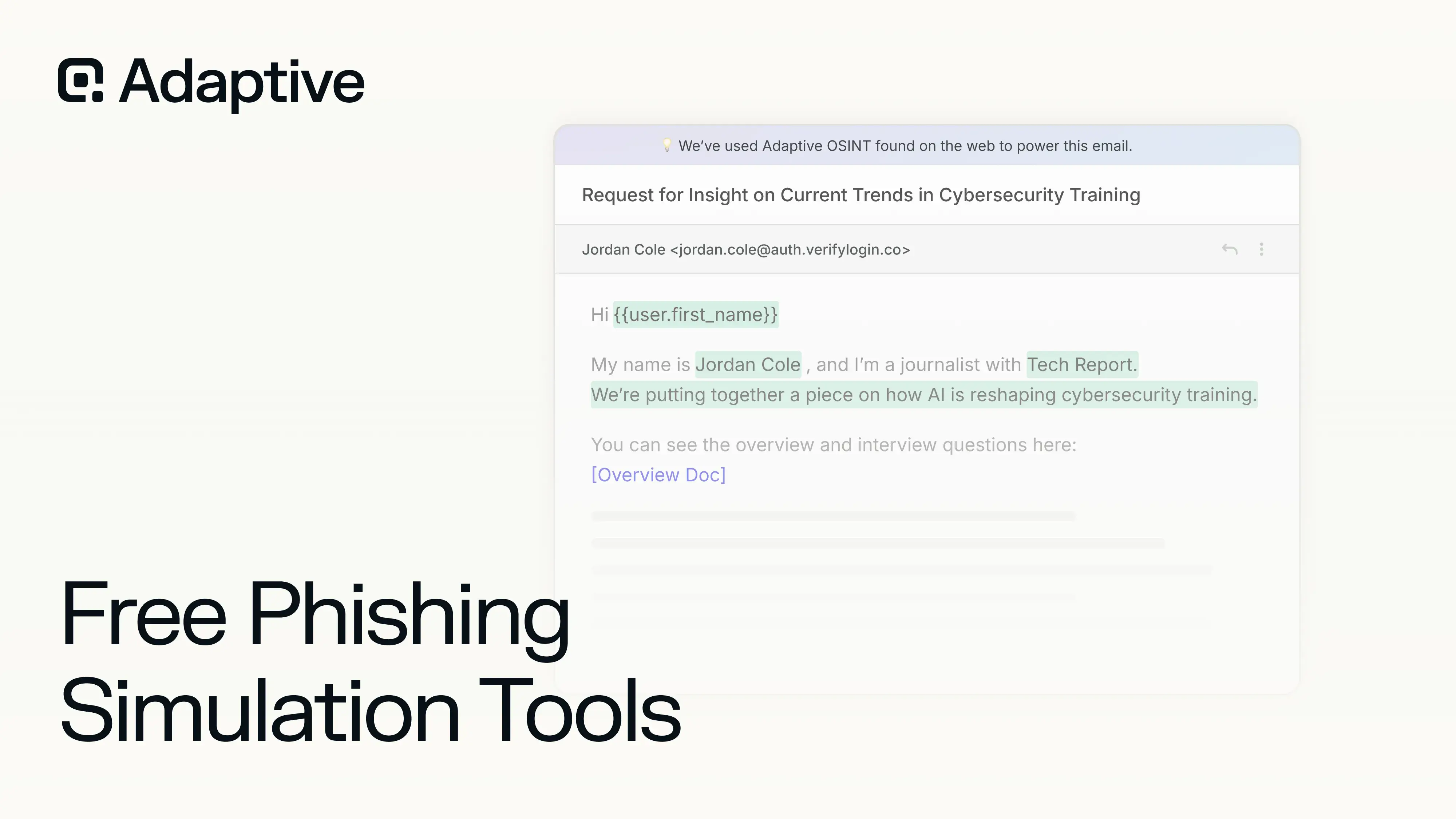
Spear phishing deserves special attention because it bypasses most technical and personal defenses. Attackers research targets using publicly available information (OSINT) from LinkedIn, company websites, and social media to craft a personalized phishing email/SMS/call.
Consider a scenario in which a recipient receives an email that appears to be from the CFO. The message looks legitimate—the headers, sender address, and tone align with established expectations. But the spear phishing signs could be so minuscule that it is hard to notice what would seem obvious in hindsight.
That is why spear phishing is so effective: it exploits trust and familiarity, not system vulnerabilities. Even the best spam filters often miss these messages, making trained, vigilant employees your strongest defense. Effective phishing awareness training is the only working defense mechanism against spear phishing attacks.
Phishing Awareness Training Component: Phishing Email Examples
Phishing awareness training programs always include a dedicated module on email phishing, given how prevalent and damaging this attack vector remains.A typical phishing email follows a recognizable pattern designed to manipulate recipients into taking action without verification.The sender address may be subtly spoofed. For example, it-support@yourcompnay.com instead of yourcompany.com.
- Greetings are often vague or generic, like "Dear User" or "Valued Customer," they can also use first names, and the message usually creating urgency or fear to pressure recipients into acting immediately
- Links are disguised as legitimate URLs, leading to fake lookalike login pages or payment portals. Attachments may request sensitive information or contain malware.
What a Real Phishing Email Actually Looks Like
For example, a classic phishing email might look like this:
Example 1:
From: IT Department Subject: Urgent: Confirm Your Account
Dear User,
We detected unusual activity on your account. Please confirm your credentials immediately to avoid suspension: [Click Here to Verify]
Example 2:
From: Payroll Subject: Tax Update Required
Hello,
Your tax information needs immediate updating to comply with new regulations. Download the attached form, complete it, and return it within 24 hours to avoid penalties.
Notice the common signals: urgency, spoofed sender addresses, vague greetings, suspicious links, and requests for credentials or sensitive information. By recognizing these patterns, recipients can identify phishing attempts before damage occurs. The following section details actionable techniques for how to spot phishing emails in 2026.
Phishing Awareness Training Against AI-Powered Cyberattacks
AI has commoditized phishing attacks long ago. Cyber attackers can now generate messages with flawless grammar, hyper-personalized content, and near-perfect contextual relevance at scale. Deepfake audio and video now allow vishing attacks that convincingly mimic executives, while AI-generated websites can host malicious login forms that are indistinguishable from the real page.
Spear-phishing campaigns that once required hours of research can be automated across thousands of targets in minutes. Traditional cues like typos, poor formatting, or generic greetings are no longer reliable flags for phishing attacks.
Relying on instinct alone to identify suspicious content is no longer reliable when AI-generated messages are virtually indistinguishable from legitimate communication. This makes out-of-band verification habits the new frontline.
Effective phishing awareness training in the current cyber threat landscape teaches organizations how to defend against AI-powered phishing attacks in 2026. Phishing prevention techniques against AI-powered cyberattacks include, but are not limited to:
- Verifying sensitive requests through out-of-band channels.
- Validating context against normal workflows and authority levels.
- Inspecting links and domains before clicking.
- Treating deepfake voice and video requests as high-risk.
- Avoiding unexpected attachments from any sender.
- Reporting suspicious messages immediately.
These habits replace outdated detection methods and create a scalable human defense layer against AI-driven attacks. For a deeper breakdown, see how to protect your company against deepfake phishing attacks.
AI-powered phishing requires AI-powered training. Adaptive Security prepares your team for modern multi-channel attacks.
Phishing Awareness Training Tips: How to Spot Phishing Emails in 2026
Since the rise of LLMs, all phishing emails have perfect grammar and some personal touch. Email phishing can no longer be identified by typographical errors alone. Phishing awareness training trains users and employees to analyze intent and inconsistencies.

Use the SLAM method (Sender, Links, Attachments, Message) to break down any suspicious email quickly:
- Sender: Check the full email address, not just the display name. Attackers spoof trusted brands or executives using lookalike domains (e.g., @rnicrosoft.com instead of @microsoft.com).
- Links: Hover over links before clicking. If the destination URL doesn't match the claimed source or uses shortened/obfuscated links, assume compromise.
- Attachments: Unexpected files, especially invoices, PDFs, or ZIP files, are high-risk. Attackers use them to deliver malware or fake login pages.
- Message: Watch for urgency, fear, or pressure. Phrases like "urgent action required" or "account suspension" are designed to bypass rational thinking. Also flag vague greetings like "Dear user" or context that don't match your role.
If you want a deeper breakdown with real-world examples, read this detailed guide on how to spot a phishing email in 2026.
How to Prevent Phishing Emails in 2026 with Phishing Awareness Training
Phishing attack prevention starts before the phishing email even reaches you. Phishing awareness training works best when paired with simple, consistent habits and baseline technical controls.
- Enable multi-factor authentication (MFA): Even if credentials are stolen, MFA blocks unauthorized access.
- Use a password manager: It prevents credential reuse and won't autofill on fake domains.
- Verify before acting: Always confirm sensitive requests (payments, password resets) through a separate channel.
- Avoid clicking unexpected links: Navigate directly to official websites instead of trusting email links.
On the technical side, organizations should implement email filtering, domain authentication (SPF, DKIM, DMARC), and threat detection systems to reduce phishing attack exposure at scale.
For a deeper look at layered defenses, see what phishing protection for emails looks like in 2026.
Phishing Awareness Training Response: What to Do If You Get a Phishing Email (Step by Step)
When a suspected phishing email is received, response speed is critical. This is where phishing awareness training turns knowledge into immediate action.
Upon detecting a phishing email, take the following steps:
- Do not click anything. Avoid all links, attachments, and buttons.
- Do not reply. Do not engage with the sender or provide any information.
- Report the email in your inbox using the built-in "Report Phishing" feature.
- Forward it to your IT or security team so they can investigate and alert others if needed.
- Log it as a security incident if you are part of an organization with a formal process.
- Forward the email to reportphishing@apwg.org to support global threat intelligence efforts.
A strong reporting culture turns one suspicious email into an early warning system for your entire organization. If your team does not have a clear process for this yet, Adaptive Security makes reporting and response a one-click action.
Your employees are your strongest defense against phishing emails. Help them report faster with Adaptive Security.
What to Do If You've Been Phished: Phishing Awareness Training Recovery Steps
While phishing awareness training reduces the chances of getting phished significantly, no phishing prevention method is foolproof. According to IBM's 2025 Cost of a Data Breach report, breaches take an average of 295 days to contain.
If you are part of an organization, employees should not attempt to resolve the incident independently – don't try to fix it yourself. For individual users who have been phished, take the following steps if you have been phished in the workplace:
- Report it to your IT support or security team immediately.
- Follow your organization's incident response plan.
- Preserve evidence. Don't delete emails or wipe your device unless instructed.
For individual users who have been phished, act immediately.
- Disconnect your device from the internet to stop any active data transfer.
- Change your passwords: starting with your email, then banking, cloud storage, and any account that reuses that password.
- Enable 2FA and MFA everywhere. Run a full malware scan and remove anything suspicious.
- If you entered financial details, contact your bank right away, explain the situation, and monitor transactions closely.
Cyber attackers move fast, and early reporting is the difference between a blocked attempt and real loss.
How to Build a Phishing Awareness Training Program For Employees and Individuals
Phishing awareness training is far more effective when structured for the long term rather than ad hoc. A clear plan reduces risks, measures progress, and reinforces learning consistently. To create a phishing awareness training program, for an organization or for yourself, you need to follow the key principles of phishing attack prevention and cybersecurity awareness training:
For Organizations:
- Assess current cyber threat risk levels and identify vulnerable teams.
- Define phishing awareness training goals, aligned with organizational threats.
- Choose a phishing awareness training platform that supports recurring, role-based phishing awareness training and simulations.
- Run baseline phishing simulations to establish the starting phish-prone percentage.
- Deliver phishing awareness training content tailored to employee roles.
- Set a cadence for phishing simulation tests and refresher lessons.
- Continuously measure results and update the phishing awareness training program based on emerging cyber threats.
For Individuals:
- Audit current habits to identify weak points like reused passwords or unverified links.
- Enable multifactor authentication (MFA) or 2FA (if MFA isn't available) on all accounts.
- Learn the SLAM method: verify Sender, Links, Attachments, and Message.
- Subscribe to a cyber threat awareness / phishing awareness newsletter to stay informed on scams.
- Test yourself with free phishing simulation tests or quizzes to reinforce learning.
How Often Do You Need Phishing Awareness Training?
Monthly phishing simulation tests, quarterly revisions, and immediate training/micro-lesson that triggers after failed attempts is the ideal frequency for phishing awareness training. Annual-only phishing awareness training programs are ineffective because phishing attacks change methods rapidly.
Set up continuous phishing simulations and automated training that adapts to employee behavior with Adaptive Security.
Individuals should revisit best practices every few months, especially after platform updates or large breach reports. According to Keepnet Labs 2026, organizations that run regular sessions reduce phishing incidents by 70%, proving consistent phishing awareness training works.
What Are the Best Practices of Phishing Awareness Training?
Individuals and employees face different types of threats and responsibilities, so the approach to phishing awareness training must be tailored. According to Hoxhunt Phishing Trends Report 2026, new hires are 71% more likely to click on phishing links within their first 90 days, highlighting the importance of early and continuous training. The same report says that phishing awareness training programs with reporting rates above 20% correlate with mature security cultures.
For Employees / Organizations:
- Integrate phishing awareness training into onboarding, because new hires are most vulnerable.
- Conduct regular phishing simulations tests that mirror real-world attacks to reinforce detection skills.
- Apply role-based training, targeting high-risk departments such as finance, executive leadership, or IT.
- Set up a visible "Report Phishing" button in email clients to encourage reporting.
- Encourage immediate reporting of suspected phishing and ensure incident response plans are clear and accessible.
- Reinforce phishing awareness training with frequent microlearning nudges, short reminders, and post-simulation follow-ups to prevent skill decay.
- Track progress and adapt content regularly to emerging threats, including AI-generated phishing and voice/sms-based cyber attacks.
For Individuals:
- Pause and think before clicking links or opening attachments, especially in urgent or unexpected messages.
- Verify requests out-of-band. Contact the sender you know directly rather than replying to the email.
- Use Multi-Factor Authentication (MFA) on all critical accounts (email, banking, cloud storage).
- Keep all devices and software updated with the latest patches and security updates.
- Use strong, unique passwords for each account and consider a reputable password manager.
- Run regular malware scans and monitor accounts for suspicious activity.
- Report phishing emails via your email provider's direct "Report Phishing" button or to authorities when appropriate.

Organizations that implement ongoing, role-based phishing awareness programs reduce susceptibility by up to 86% within a year, according to KnowBe4 Phishing by Industry Benchmarking Report 2025.
Can Phishing Awareness Training Stop Ransomware Attacks?
Yes, phishing awareness training can stop ransomware attacks. Because most ransomware starts with a phishing email.
If no one clicks on the phishing email, the ransomware attack never lands. Phishing awareness training interrupts the primary attack vector before execution.
According to Hoxhunt's Phishing Trends Report 2026, 54% of ransomware attacks originate from phishing attempts. The initial phishing email is the entry point to credential theft, malicious attachments, or payload delivery.
Phishing awareness training prevents ransomware attacks by training employees to recognize the trap, question the request, and report it before execution.
How to Measure the Success of Your Phishing Awareness Training Program
The success of phishing awareness training programs isn't measured by completion rates, or practice frequency. You measure behavioral change under pressure using phishing simulation tests. The key metric is the response when a real phishing attack lands in the inbox.
To measure the success of your phishing awareness training program, look out for the metrics below:
- Phishing simulation click rate measures how many users/employees fall for phishing simulations. According to KnowBe4's 2025 Phishing by Industry Benchmarking Report, the industry baseline starts around 30%. If the click rate isn't consistently dropping over time, then the phishing awareness training program isn't working.
- Phishing attack report rate measures what percentage of users/employees report suspicious phishing emails/texts. According to Hoxhunt Phishing Trends Report 2026, organizations with reporting rates above 20% consistently show strong security culture. A low report rate, compared to the number of phishing simlulation tests, is an indicator that employees either don't recognize threats, or don't feel the responsibility of reporting them.
- Individual risk scoring is a system that marks the users who repeatedly fail simulations as "high risk," and vice versa for "low risk." For high risk individuals, point-of-error immediate micro-lesson keeps them from repeating the same mistake again. This can be done manually by tracking phishing simulation click rates, and sending over relevant training.
For individual risk scoring and automated feedback loops, try out Adaptive Security's Dynamic Risk Scoring today.
- Incident response time measures how quickly employees report a suspected (or successful) phishing attempt. Faster reporting allows faster containment of damage.
- Training completion rate, while not as indicative of success as other metrics, still shows participation rates. It is impossible to get to other metrics if the completion rate itself isn't 100%. Still, a high completion rate with poor simulation results is a failure of phishing awareness training.
If you want a deeper breakdown, see how to measure the success of your phishing awareness training program.
What Is the ROI of Phishing Awareness Training for Businesses?
The ROI for phishing awareness training is straightforward. A mid-tier phishing awareness training platform typically runs between $10 and $40 per employee per year. For a 500-person company, that is roughly $20,000 annually.
But the ROI of phishing awareness training extends beyond breach cost avoidance. Cyber insurers are increasingly treating security awareness programs as a condition of coverage. Companies without documented phishing awareness training programs are seeing higher premiums, narrower coverage terms, or outright rejections at renewal. While not from a data breach, the cost is still damaging, with the added risk of an actual data breach later on.
There's also the cost of incident recovery that isn't mentioned in the phishing awareness training ROI. When a phishing attack succeeds, the breach cost, credential theft, ransomware, or wire fraud is only part of the equation. Response and mitigation, legal review, regulatory notification requirements, and productivity loss, all count, and can double the initially estimated damage.
For most businesses, the per-employee cost of training gets recovered the moment it prevents a successful phishing attempt from escalating into a full incident.
Common Issues & Pain Points of Phishing Awareness Training Programs
Most phishing awareness training programs fail because the scope of their training is too shallow. The biggest failure point for phishing awareness training programs is one-time annual training.
According to a 2025 University of Chicago study, phishing awareness course completion showed no meaningful reduction in phishing susceptibility. In fact, repeated static phishing awareness training was linked to an 18.5% increase in failure rates. If your phishing awareness course runs once a year, it is already outdated.
Another major issue is click-shame culture. When employees are punished or embarrassed for failing phishing simulation tests, they stop reporting incidents. That kills your early-warning system. Strong phishing awareness training programs treat every failure as a learning opportunity, rewarding detection and incident response.
Generic, one-size-fits-all phishing awareness courses also break effectiveness. A finance employee handling wire transfers faces completely different risks than a junior marketing assistant. Phishing awareness training that ignores role-specific threats fails to prepare people for real attacks.
Then there's the lack of a feedback loop after simulations. If someone clicks a phishing simulation and gets no immediate feedback or explanation, nothing changes. According to SoSafe 2025 research, point-of-error training outperforms all other methods because it corrects behavior in real time.
Fix the gaps in your training program with real-time feedback and tailored learning that actually changes behavior.
Finally, many programs collapse due to lack of leadership buy-in. It is a trickier problem to solve compared to other pain points. If executives don't take phishing awareness training seriously, employees won't either.
This is especially dangerous because executives are the prime targets. Grand View Research Spear Phishing Market Report 2024 identified that spear phishing success rates for leadership roles exceed 39%.
What separates mediocre phishing awareness training programs from effective ones is frequency, relevance, feedback, and culture. Without those, phishing awareness training becomes a checkbox to complete instead of a phishing attack prevention strategy.
If you want a practical breakdown of what actually works, you can download our free guide on phishing awareness training.
Common Misconceptions in Phishing Awareness Training
The reason most people fail phishing simulation tests isn't because they're careless during their phishing awareness training. Rather, they fail because they believe outdated assumptions about phishing attacks that cyber attackers still actively exploit in 2026.
These are the common misconceptions that break phishing awareness training in practice:
- "Spam filters catch everything" - While spam filters catch a lot of email phishing by default, the cleverly crafted ones still slip into your inbox without raising any alarms. Those phishing emails are the ones that test an employee's phishing awareness training. According to Zensec 2025, AI-generated phishing emails are now 24% more effective than human-written ones, meaning they look more convincing than what most people are trained to detect.
- "Only non-technical people fall for phishing" is a common assumption among the ones working in the tech industry. On the contrary, spear phishing specifically targets experienced employees and executives using real work context. The assumption that technical people know phishing when they see it, and thus are immune to it, is false. There is no substitute for phishing awareness training for any employee or user.
- "I'll know a phishing email when I see it" - This sentiment mirrors the one mentioned previously. Not only is it more dangerous, but it is also misleading, as it assumes that anyone can detect phishing attacks without phishing awareness training. Phishing scams don't contain obvious typos or exaggerated claims anymore. They are more subtle, exactly like the ones you would receive from a legitimate sender, which is why organizations and employees need phishing awareness training more than ever. An individual will not necessarily know a phishing email when they see it, except when they are trained.
- "Phishing only happens via email" - While email phishing is the most commonly known phishing method, SMS phishing (smishing), voice call phishing (vishing), and social media impersonation have been prevalent for a while now. According to Deepstrike 2025, vishing attacks surged 442% in a single year due to AI voice cloning.
These misconceptions about phishing awareness training are exactly what cyberattackers rely on. An effective phishing awareness training program doesn't just train you tactically, it also changes your mindset around how to prevent phishing attacks.
Change how your team thinks about phishing. Adaptive Security's microlearning builds lasting security habits, not just awareness.
Phishing Awareness Training Clarified: What's the Difference Between Spam vs. Phishing?
Spam is unsolicited bulk email, annoying but usually harmless. It is mainly for advertising, not for tricking you.
Phishing is a targeted cyberattack that attempts to steal passwords, money, or private information by pretending to be a trusted person or company. It uses lies, urgency, and pressure to make you act.
Confusing the two is risky. If people call phishing "just spam" and ignore or fail to report it, attackers get more time to succeed.
Phishing Awareness Training Clarified: What's the Difference Between Spoofing vs. Phishing?
Spoofing is a technique where the cyberattack appears to come from a legit sender address, domain, or website to make it look legitimate. Phishing is the cyberattack that uses spoofing and other techniques to trick the target into giving away credentials, information, or access.
Example: a spoofed email that looks like it is from your bank is the technique; the request to "verify your account" through a fake login page is the phishing attack.
The Future of Phishing Awareness Training
Phishing attacks have shifted from generic mass emails to AI-generated, hyper-personalized campaigns that use OSINT, perfect language, and multi-channel delivery.

To keep up with the fast evolution of AI-powered phishing attacks, phishing awareness training programs have shifted from static, annual education to continuous, realistic, behavior-oriented cybersecurity awareness training.
Here are the standards that are the future of phishing awareness training:
AI-Powered Personalized Phishing Awareness Training
Phishing awareness training is no longer based on one lesson for everyone. AI-powered phishing awareness training delivers content based on role, behavior, and risk exposure. Employees receive scenarios that reflect their role-specific real workflows, not generic examples. This improves relevance and increases retention because training matches the exact threats each user is likely to face.
Real-Time Phishing Awareness Training at the Moment of Error
Besides regular micro-training and refreshers, phishing awareness training is moving to the point of action, too. When a user clicks or interacts with a suspicious message, they receive immediate, contextual feedback. According to Carnegie Mellon research cited in SoSafe 2025, point-of-error training reduces phishing susceptibility by 40% on average.
Continuous Microlearning Over Annual Phishing Awareness Training
Annual phishing awareness training fails because phishing scams evolve faster than yearly refresh cycles. Continuous microlearning delivers short, frequent training that reinforces phishing attack prevention behavior over time. According to Hoxhunt Phishing Trends Report 2026, phishing detection skills decline within four to six months without repeated practice and phishing simulation tests.
Phishing Awareness Training Gamified to Reinforce Security Behavior
Modern phishing awareness training programs use gamification to increase reporting rates and engagement. This includes rewarding correct actions (such as identifying and reporting phishing emails quickly).
Integration with SIEM and SOAR Platforms
Phishing awareness training is integrating directly into security operations. Reported phishing emails become actionable signals that trigger automated classification and remediation. The data from phishing awareness training is now part of the detection and response pipeline of organizations.
How Adaptive Security Approaches Phishing Awareness Training
Adaptive Security approaches phishing awareness training as a continuous behavioral system, not a compliance task. The platform focuses on measurable outcomes such as reduced click rates, faster reporting, and improved risk scores across teams.

Adaptive Security's phishing awareness training system connects four stages of cyber security awareness training into a single loop.
- Phishing simulations identify high-risk behavior.
- Phishing awareness training addresses knowledge gaps.
- Phish triage reinforces the reporting of phishing attacks and automates response.
- Risk monitoring tracks improvement over time, assigning risk scores with "Dynamic Risk Scoring".
This creates a closed feedback loop where every action leads to measurable progress in their phishing awareness training.
And it doesn't end there. When a user fails a phishing simulation, they receive immediate microlearning tied to that exact mistake. This timing increases retention and directly improves behavior during future phishing attacks.
"We've actually got our employees reaching out to us about the training, and the information is sticking." - Jonathan Aluveaux, Plaid
Our phishing awareness training is role-based and context-aware. Employees receive scenarios based on their responsibilities, communication patterns, and potential exposure to threats. We run targeted simulations, such as invoice fraud for finance teams, deepfake impersonation for executives, and realistic credential-harvesting and BEC exercises for customer-facing and operations staff. That is what makes the knowledge stick and keeps learners engaged.
Adaptive Security also mimics how modern attackers operate. Phishing simulations cover email, SMS, and voice phishing, including AI-generated deepfake scenarios. You get only the relevant, latest phishing simulations.
Turn phishing awareness training into measurable risk reduction—not just a compliance exercise—with Adaptive Security.
Phishing Awareness Training: Frequently Asked Questions
How Effective Is Phishing Awareness Training for Employees?
Well-run phishing awareness training programs reduce employee click rates by 60-80%. Effectiveness relies on realistic, frequent simulations and immediate post-click feedback. Annual certification training alone is largely ineffective.
What Are the Most Common Types of Phishing Attacks to Watch Out For?
Through phishing awareness training, employees learn to spot common threats: email phishing, personalized/generic mass emails; spear phishing, highly targeted phishing attacks; smishing, phishing via SMS; vishing, voice calls impersonating trusted sources; whaling, phishing targeting executives; and clone phishing, duplicating legitimate emails with malicious links.
Are Phishing Simulations Better Than Traditional Phishing Awareness Training?
The best approach combines both. Phishing awareness training that includes simulations tests reflexes and reinforces knowledge, while classroom or video lessons provide essential context. Simulations without education creates shame; and education without practice doesn't build instincts. Both need to be implemented to enforce behavioral change.
Is Phishing Awareness Training Mandatory for Companies?
It depends on industry and jurisdiction. HIPAA, PCI-DSS, ISO 27001, and GDPR strongly imply or require phishing awareness training, and some U.S. states are moving toward explicit mandates. Even where not legally required, cyber insurers often make it compulsory.
What Are Some Free Resources for Phishing Awareness Training?
Free resources include CISA's online guides, Google's Phishing Quiz, and free awareness modules. These tools support phishing awareness training at a basic level, but they lack the simulation, reporting, and reinforcement of dedicated platforms like Adaptive Security.
What Is a Phishing Email Checker?
A phishing email checker scans incoming messages for suspicious links, spoofed sender domains, and malicious attachments. While tools like Microsoft Defender and Google Safe Browsing assist phishing awareness training, they catch only known threats; human vigilance is still essential for new or AI-generated phishing attacks.
Phishing Awareness Training Action Steps: What to Do Next
- Phishing awareness training reduces risk when it changes behavior, not when it checks a compliance box. Ongoing simulations and reinforcement matter more than one-time training.
- AI-powered phishing attacks are now precise, scalable, and harder to detect. Grammar and formatting are no longer reliable signals. Phishing awareness training is mandatory.
- Employees are your first line of defense. Faster reporting of phishing attacks and better decision-making directly reduce data breach impact.
- Continuous microlearning and real-time feedback outperform annual training. Phishing detection skills improve with repetition and decay without it.
- Measurement defines success. Click rates, report rates, and time-to-report show whether phishing awareness training is working.
Phishing awareness training works when it is consistent, relevant, and tied to real-world behavior. Start by evaluating where you and your organization stand today. Check whether your current approach reflects how modern phishing attacks actually work. If not, it is time to assess real world cyber threats first.
No time to build a custom phishing awareness training program? Check out Adaptive Security's pre-built, hyper-personalized program built for organizations.
Research / Stats
Statistics
(bold = must use, italic = skippable, rest = general)
- According to Verizon DBIR 2025 (Verizon, published April 2025), phishing remains the top cyber threat vector, with 80-95% of breaches starting via phishing attacks.
- According to Verizon DBIR 2025 (Verizon, published April 2025), 60% of breaches involved the human element, with phishing accounting for 16% of initial breach vectors and stolen credentials used in 22% of attacks.
- According to Cofense Report "The New Era of Phishing: Threats Built in the Age of AI" (Cofense, February 2026), malicious email attacks occurred every 19 seconds in 2025, doubling from 42 seconds in 2024 due to AI acceleration.
- According to Keepnet Labs "2025 Phishing Statistics" (Keepnet Labs, updated January 2026), global daily phishing emails reached about 4 billion in 2025, comprising 1.2% of total email traffic (citing Anti-Phishing Working Group data).
- According to IBM Cost of a Data Breach Report 2025 (IBM, July 2025), average phishing breach costs hit $4.88 million in 2025 (phishing vector average $4.8M).
- According to IBM Cost of a Data Breach Report 2025 (IBM, July 2025), organizations with strong employee training programs lowered their average breach costs from $5.10 million to $4.15 million, a saving of $950,000 per incident.
- According to Keepnet Labs "[Updated 2026] Security Awareness Training Statistics" (Keepnet Labs, March 2026), large organizations face $14.8 million annual phishing costs, with $164 per stolen record.
- According to KnowBe4 "Phishing by Industry Benchmarking Report 2025" (KnowBe4, May 2025), organizations reduce phishing susceptibility by 40% in 90 days and 86% in a year via ongoing training, dropping baseline phish-prone percentage from 33.1%.
- According to KnowBe4 "Phishing by Industry Benchmarking Report 2025" (KnowBe4, May 2025), trained users are 30% less likely to click phishing links, with click rates falling from 42% to 4.1% in large firms after one year.
- According to Keepnet Labs "[Updated 2026] Security Awareness Training Statistics" (Keepnet Labs, March 2026), security awareness training cuts overall risks by 70% and incidents by 70% with regular sessions.
- According to Ponemon Institute research (cited across multiple 2024-2025 industry reports), security awareness training delivers approximately a 50x ROI, with well-designed programs reducing phishing-related breach risk by up to 70%.
- According to Hoxhunt Phishing Trends Report 2026 (Hoxhunt), AI phishing surged 14x by end-2025, reaching 56% of attacks; credential phishing rose 703% in H2 2024.
- According to Hoxhunt Phishing Trends Report 2026 (Hoxhunt), callback phishing grew 500% in Q4 2025; 54% of ransomware starts with phishing.
- According to Hoxhunt Phishing Trends Report 2026 (Hoxhunt), new hires are 71% more likely to click phishing links in the first 90 days.
- According to Hoxhunt Phishing Trends Report 2026 (Hoxhunt), phishing reporting rates above 20% are associated with mature security culture programs; skills fade after 4-6 months without reinforcement, and simulations outperform traditional training with up to 9x reporting gains (citing CIRA and TitanHQ).
- According to a 2024 meta-analysis of 42 phishing simulation studies and Carnegie Mellon University research (cited in SoSafe 2025), point-of-error training, delivered immediately after a simulated phishing click, reduces susceptibility by an average of 40%, significantly outperforming all other training delivery methods.
- According to a 2025 University of Chicago study of 19,500 healthcare employees (cited in Brightside AI 2025), annual training completion showed no significant correlation with reduced phishing failures, and UC San Diego researchers found that each additional static training session completed was associated with an 18.5% increased likelihood of failing future phishing attempts.
- According to Zensec "Phishing Statistics 2025-2026" (Zensec, 2025), 82.6% of phishing emails detected between September 2024 and February 2025 utilized AI, a 53.5% year-on-year increase, and 92% of polymorphic phishing attacks use AI to achieve unprecedented scale.
- According to Zensec "Phishing Statistics 2025-2026" (Zensec, 2025), AI-powered attacks improved from being 31% less effective than human-crafted phishing emails in 2023 to 24% more effective by March 2025.
- According to Zensec "Phishing Statistics 2025-2026" (Zensec, 2025), ransomware delivery via phishing surged 57.5% between November 2024 and February 2025, with 45% of all ransomware attacks delivered via phishing emails.
- According to Deepstrike "Vishing Statistics 2025" (Deepstrike, 2025), voice phishing surged 442% in 2025 as AI-cloned voices enabled an estimated $40 billion in global fraud, with over 10% of banks having lost more than $1 million each to a deepfake call.
- According to recent threat intelligence data (cited in Right-Hand AI, 2025), deepfake-enabled vishing surged by over 1,600% in Q1 2025 compared to the end of 2024.
- According to NIS2 Directive implementation records (effective October 17, 2024) and DORA compliance requirements (effective January 17, 2025), EU organizations across critical infrastructure and financial services are now legally mandated to implement ongoing security awareness training, with NIS2 non-compliance fines reaching €10 million or 2% of global annual turnover.
- According to IBM Cost of a Data Breach Report (IBM), data breaches from phishing take 295 days to contain (average lifecycle).
- According to Keepnet Labs "[Updated 2026] Security Awareness Training Statistics" (Keepnet Labs, March 2026), only 52% of firms do anti-phishing training; 3% report phishing.
- According to FBI Internet Crime Complaint Center (IC3) 2024 Annual Report (FBI, published 2025), Business Email Compromise (BEC) phishing caused $2.77 billion in reported losses in 2024, across 21,442 complaints. Since 2015, total BEC losses have exceeded $17.1 billion.
- According to Keepnet Labs "2025 Vishing Response Report" (Keepnet Labs, 2024), 70% of organizations unknowingly share sensitive information during vishing simulations, and vishing attacks cost organizations an average of $14 million annually.
- According to KnowBe4 "Phishing by Industry Benchmarking Report 2025" (KnowBe4, May 2025) and HIPAA Journal data (cited in Cobalt 2026), healthcare organizations are more vulnerable to phishing than any other major industry, with 41.9% of organizations susceptible, compared to 39.2% of insurance providers and 36.5% of retail and wholesale providers.
- According to Grand View Research Spear Phishing Market Report (October 2024), spear-phishing success rates exceed 39% for executives in 2025; the market grew from $1.75B in 2024 to a projected $4.84B by 2033.
- According to Hoxhunt Phishing Trends Report 2026 (Hoxhunt) and Verizon DBIR 2024-2025 data, the global benchmark for users who report phishing simulations sits at around 20%, and organizations achieving above this threshold consistently have implemented behavior-change programs rather than one-off training.
- According to StationX "Top Phishing Statistics 2026" (StationX, February 2026), financial institutions face 27.7% of attacks, SaaS 17.7%, and social media 10.4%; after 12 months of training, finance sector success rates hit 74%, healthcare and retail approximately 61% (citing Hoxhunt and KnowBe4).
- According to a large-scale simulation study of 31,000 participants (cited in SoSafe 2025), after 12 weeks of phishing simulations, 66% of users successfully resisted credential-based attacks.
- According to ETH Zurich research (2024, cited in Mantra Security), regular "nudges", brief, frequent reminders about phishing dangers, drove training effectiveness more than training content quality alone, validating frequency over volume.
- According to Zensec "Phishing Statistics 2025-2026" (Zensec, 2025), QR code phishing attacks increased by 400% between 2023 and 2025, with Mastercard the most targeted brand at 14,233 malicious QR codes, followed by Microsoft at 11,796.
- According to Verizon DBIR 2025 (Verizon, published April 2025), ransomware was present in 44% of all breaches, a 37% increase from 2024, and was involved in 88% of breaches affecting small and midsize businesses.
- According to Infrascale "2025 Cybersecurity Survey" (Infrascale, 2025), 53% of US senior technology leaders say employees are the least prepared to handle phishing threats, and 96% of executives believe organization-wide training would help reduce cyberattacks.
- According to Gartner research (cited in Infrascale 2025), 68% of security leaders say low engagement is one of the biggest challenges in phishing training program design, and 77% cite lack of accountability as the biggest barrier to employee participation.




As experts in cybersecurity insights and AI threat analysis, the Adaptive Security Team is sharing its expertise with organizations.
Contents